When hesitant on the applicability of a CSCF control to a particular component? What steps should you take? (Choose all that apply.)

Which operator session flows are expected to be protected in terms of confidentiality and integrity? (Choose all that apply.)

What are the possible impacts for a SWIFT user to be non-compliant to CSP? (Select the two correct answers that apply)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
How are online SwiftNet Security Officers authenticated? (Select the correct answer)
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
The objective of the Customer Environment Protection control is to separate the user's Swift infrastructure which restricts malicious access from the external world and from the General IT environment of the Swift user.

The outsourcing agent of the SWIFT user provided them with an independent assessment report covering the CSP components in their scope, and using the latest CSCF version for testing. Is it enough to support the CSP attestation for the outsourced components? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Can an assessor re-use an ISAE 3000 report dating back 2 years to support an independent assessment?
What are the conditions required to allow reliance on the compliance conclusion of a control assessed in the previous year? (Select all answers that apply)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Compliance to 2.9 Transaction Business Controls can be obtained through different ways. Which of the following one does not ensure compliance?
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Which authentication methods are possible on the Alliance Interfaces? (Choose all that apply.)

The SWIFT HSM Box must be hardened at the system level by the SWIFT user owning the equipment.
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Which of the following infrastructures has the smallest SWIFT footprint? (Select the correct answer)
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
Application Hardening basically applies the following principles. (Choose all that apply.)

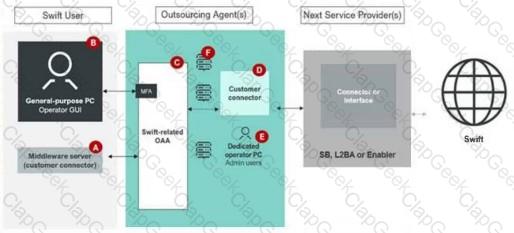
Using the outsourcing agent diagram. Which components must be placed in a secure zone? (Choose all that apply.)

Is the restriction of Internet access only relevant when having Swift-related components in a secure zone?

The SWIFT user’s first line of defence has performed a detailed self-assessment demonstrating an adequate compliance level to each of the applicable controls. As an assessor, may I fully rely on this analysis if the SWIFT user can demonstrate that their conclusion was based on a valid testing approach? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
What does the CSCF expect in terms of Database Integrity? (Select the two correct answers that apply)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
The SWIFT VPN boxes are located between the Messaging and Communication interface.
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
The Internal Audit and an external assessment company are both involved in a SWIFT user’s assessment. Both have shared control assessments to cover the full scope (meaning two separate assessment teams). Who needs to provide a completion letter? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
Select the correct statement about SWIFT Alliance Cloud.
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
The messaging operator in Alliance Lite2… (Select the two correct answers that apply)
•Connectivity
•Generic
•Products Cloud
•Products OnPrem
•Security
What are the conditions required to permit reliance on the compliance conclusion of a control assessed in the previous year? (Choose all that apply.)
The Alliance Web Platform Administrator uses both the GUI and command line to perform configuration and monitoring tasks on AWP SE.

Which encryption methods are used to secure the communications between the SNL host and HSM boxes?

May an assessor rely on an ISAE 3000 report dating back 2 years to support a CSP independent assessment? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
What is the purpose of the High-Level Test Plan (HLTP) provided by SWIFT? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
A SWIFT user has had part of controls assessed by their internal audit department, and the other remaining controls using an external assessor company. Is this acceptable? (Select the correct answer)
•Swift Customer Security Controls Policy
•Swift Customer Security Controls Framework v2025
•Independent Assessment Framework
•Independent Assessment Process for Assessors Guidelines
•Independent Assessment Framework - High-Level Test Plan Guidelines
•Outsourcing Agents - Security Requirements Baseline v2025
•CSP Architecture Type - Decision tree
•CSP_controls_matrix_and_high_test_plan_2025
•Assessment template for Mandatory controls
•Assessment template for Advisory controls
•CSCF Assessment Completion Letter
•Swift_CSP_Assessment_Report_Template
What type of control effectiveness needs to be validated for an independent assessment?



