When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21.
The shard cache technology will wait for the arrival of the first shard packet, and then reassemble and decrypt all the packets, and then do subsequent processing by the device to ensure that the session can proceed normally in some application scenarios.
The RADIUS protocol specifies how to pass user information, billing information, authentication and billing results between the NAS and the RADIUS server, and the RADIUS server is responsible for receiving the user's connection request, completing the authentication, and returning the result to the NAS.
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
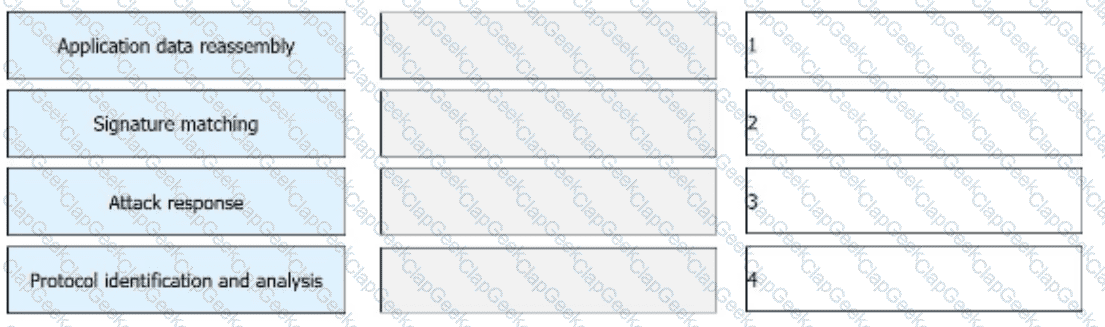
The IPS detects and analyzes all packets passing through a device and determines whether to permit or block the packets in real time based on the comprehensive detection mechanism. Sort the following steps into the correct order based on the basic implementation mechanism of the IPS.
____- The goal is to provide a rapid, composed and effective response in emergency situations, thereby enhancing the ability of the business to recover immediately from a disruptive event.[fill in the blank]*
The network environment is becoming more and more complex, and network security incidents occur frequently. While accelerating the construction of informatization, enterprises must not only resist external attacks, but also prevent internal management personnel from being involved in data leakage and operation and maintenance accidents due to operational errors and other issues. Which of the following options might reduce operational risk?
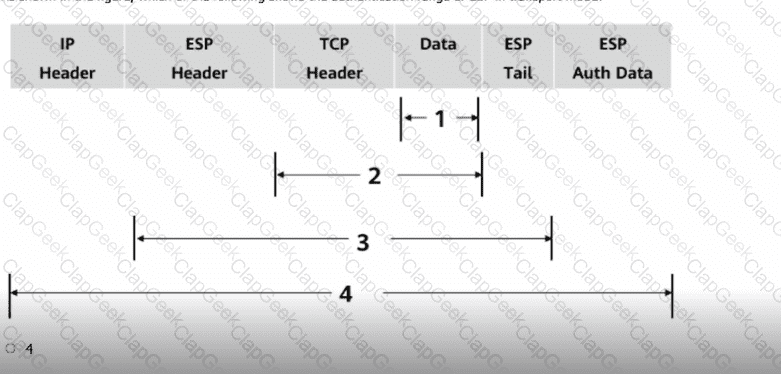
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
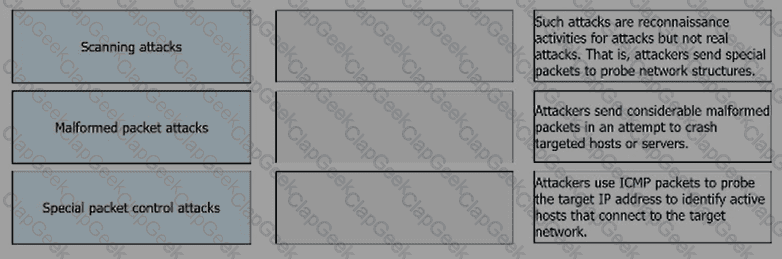
Match the following single-packet attack types with their corresponding descriptions.
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
Which of the following statements is correct about characteristics of a firewall?
The following description of the construction of a digital certificate, which item is wrong
Social engineering is a means of harm such as deception, harm, etc. through psychological traps such as psychological weaknesses, instinctive reactions, curiosity, trust, and greed of victims ( )
In asymmetric encryption algorithms, only public keys can be used to encrypt data, and private keys are used to decrypt data. This process is irreversible.
What is correct about the following description of device management in the operating system?
IKE SA is a one-way logical connection, and only one IKE SA needs to be established between two peers.
The trigger authentication method for firewall access user authentication does not include which of the following?
Using the ___ method of the Web proxy, the virtual gateway will encrypt the real URL that the user wants to access, and can adapt to different terminal types.[fill in the blank]*
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.
Devices that need to provide network services externally, such as WWW servers and FTP servers, can be placed in the DMZ.
In cases where some configurations alter existing session table entries and want them to take effect immediately, you can regenerate the session table by clearing the session table information. All session table information can be cleared by executing the _____firewall session table command.
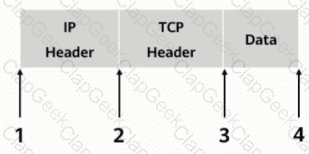
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.
An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
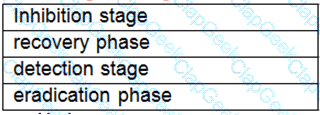
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution.[fill in the blank]*
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.
In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
For which of the following parameters can the packet filtering firewall filter?
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
Which of the following is the correct sequence for incident response management
1. Detection 2 Report 3 Mitigation 4 Lessons learned 5 Fix 6 Recovery 7 Response